Four types of fake key attacks. Each diagram represents Alice
Download scientific diagram | Four types of fake key attacks. Each diagram represents Alice (left), her contacts (right), and an adversary (center). The green lines represent secure connections; the red lines represent compromised connections. Note that in each situation, there may be other pairs of clients communicating securely that are not shown. from publication: Automatic Detection of Fake Key Attacks in Secure Messaging | Popular instant messaging applications such as WhatsApp and Signal provide end-to-end encryption for billions of users. They rely on a centralized, application-specific server to distribute public keys and relay encrypted messages between the users. Therefore, they prevent | Automatism, Security and Server | ResearchGate, the professional network for scientists.
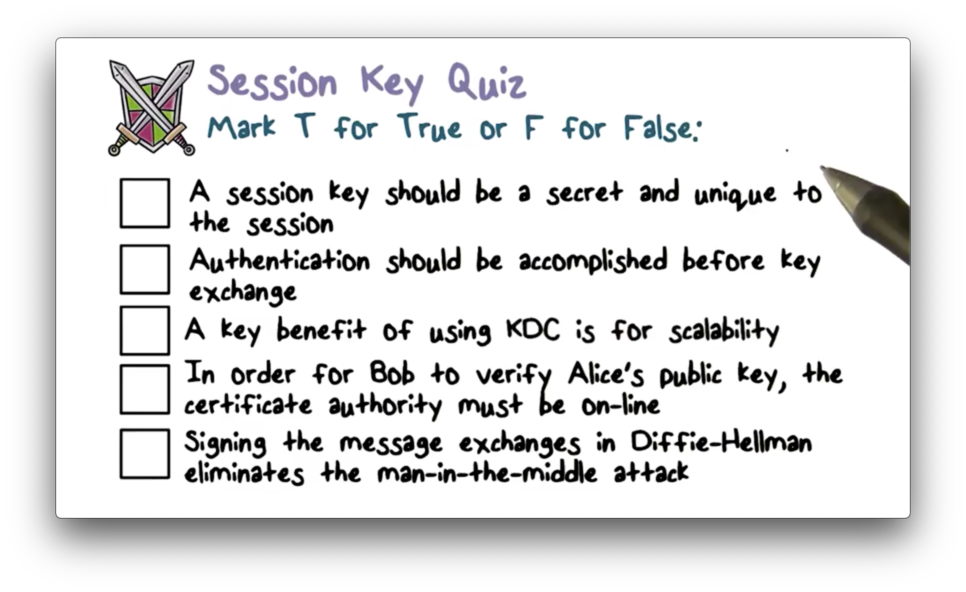
Security Protocols - OMSCS Notes
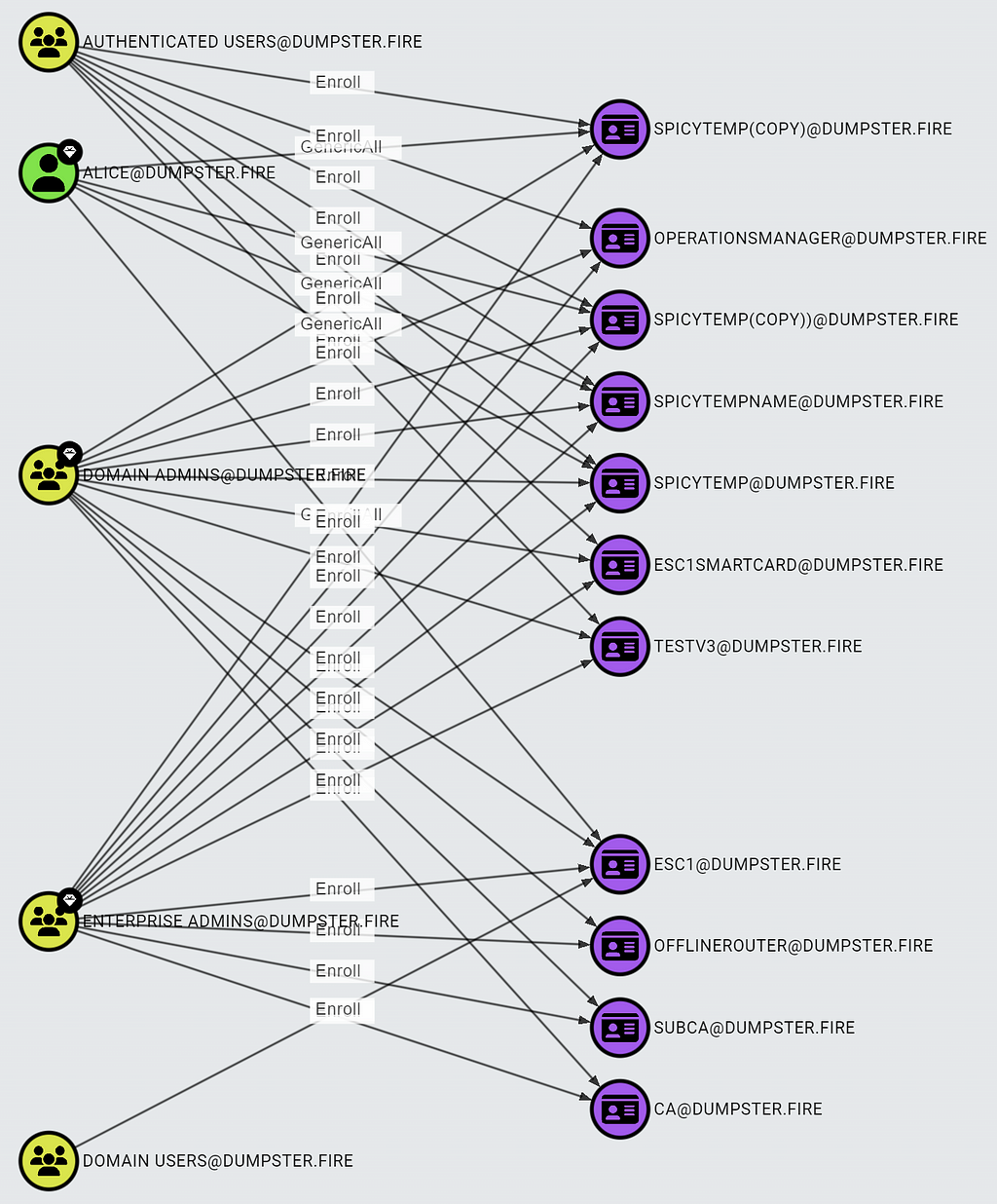
ADCS Attack Paths in BloodHound — Part 1 - Security Boulevard

PDF) Automatic Detection of Fake Key Attacks in Secure Messaging
Networking 101: Transport Layer Security (TLS) - High Performance Browser Networking (O'Reilly)
Phishing and impersonation attacks (A 8 ) being executed, while

High-rate measurement-device-independent quantum cryptography

Public-Key Cryptography Brilliant Math & Science Wiki

Daniel Zappala's research works Brigham Young University - Provo

10 Common Website Vulnerabilities: Security Tips
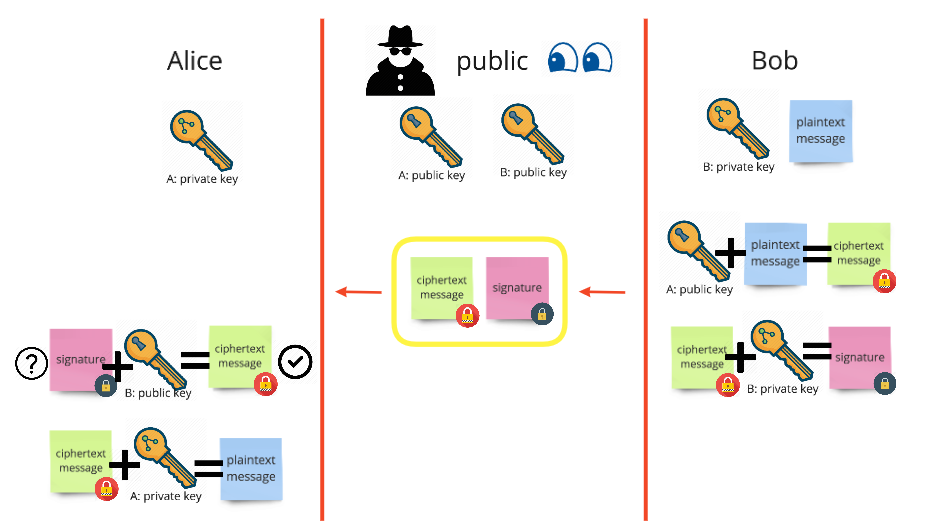
What are encryption keys and how do they work? 🔐, by Dominic Fraser, CodeClan








