What is a Buffer Overflow Attack Types and Prevention Methods
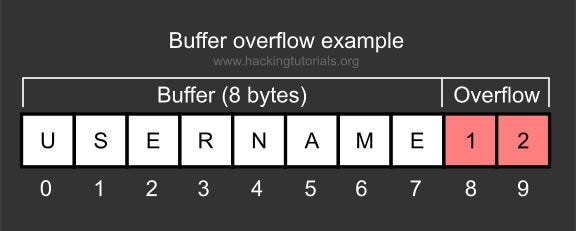
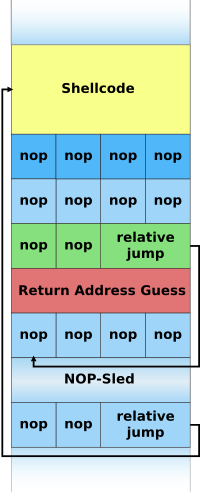
Attackers exploit buffer overflow issues to change execution paths, triggering responses that can damage the applications and exposes private information.

PDF) Buffer Overrun: Techniques of Attack and Its Prevention
Stack Based Buffer Overflow Practical For Windows (Vulnserver), by Shamsher khan

What is a Buffer Overflow, Attack Examples and Prevention Methods

BUFFER OVERFLOW ATTACK AND HOW IT IS USED TO ATTACK YOUR NETWORK
Buffer overflow - Wikipedia

Introduction to Buffer Overflow Attacks » Triaxiom Security

Buffer Overflow: Attack, Types And Vulnerabilities Explained

How to Prevent Buffer Overflow - Parasoft

nmap cheet sheet 0.6.pdf - Nmap Cheat Sheet Scan Techniques Target Specification Switch -iL -iR -exclude Example nmap 192.168.1.1 nmap 192.168.1.1
Solved 1. Explain Exception Handling in C#. 1.1 What is, exceptions c#

The 3 Types of Buffer Overflow Attacks and Prevention Tips - Packt - SecPro

How to Protect Against Buffer Overflow Attack

ROP and Buffer Overflow: A Deadly Duo in Cybersecurity Exploits - FasterCapital